February 25, 2026

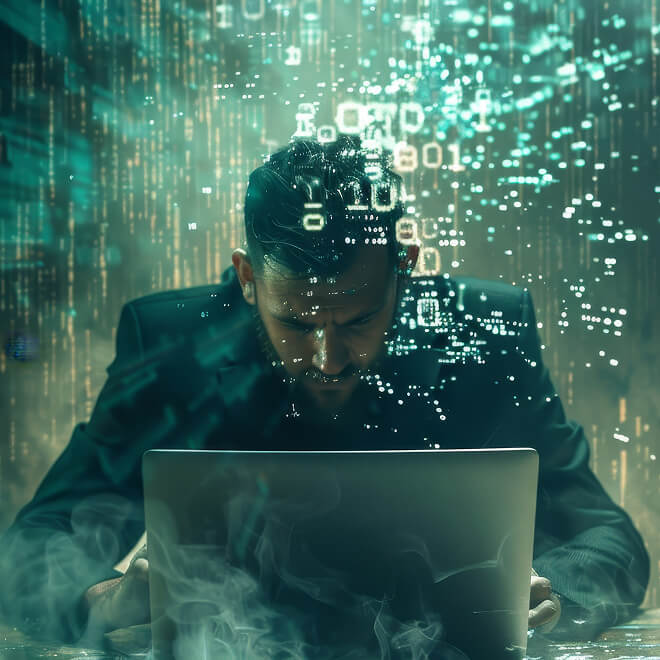
Modern adversaries do not operate annually. They operate continuously—probing, adapting, pivoting, and evolving in real time. Meanwhile, organizations still rely on episodic security assessments that provide only a snapshot of risk at a single point in time.
The gap between how attackers operate and how defenders test has never been wider.
Traditional pen tests suffer from three structural limitations:
1. Static Scope in a Dynamic Environment
Infrastructure changes weekly. Cloud configurations shift daily. Code deploys hourly. An annual assessment cannot account for that velocity.
2. Compliance-Driven Mindset
Too often, testing becomes an exercise in satisfying an audit requirement rather than measuring real adversarial exposure.
3. Limited Threat Context
Many engagements test generic vulnerability classes rather than adversary behaviors that are actively targeting the organization’s sector.
The result? A report that may be technically accurate—but operationally outdated within months.
Threat actors continuously:
They leverage automation, AI, and intelligence feeds to reduce their cycle time. If your testing model doesn’t account for that, you’re measuring yesterday’s risk.
Continuous resilience is not “more scans.” It is not “quarterly pen testing.”
It is an operating model built around:
Instead of asking, “Did we pass the test?”
You ask, “If an adversary targeted us this week, what would happen?”
The goal shifts from generating findings to mapping exposure:
Continuous adversarial testing aligns your security program with real-world attacker behavior—not theoretical weaknesses.
The organizations that will outperform in the next decade are those that:
The one-off pen test isn’t “dead” because it lacks value.
It’s dead because it lacks context and continuity.
Resilience today is not a point-in-time achievement.
It is a continuously tested capability.
.png)
Chief Technology Officer